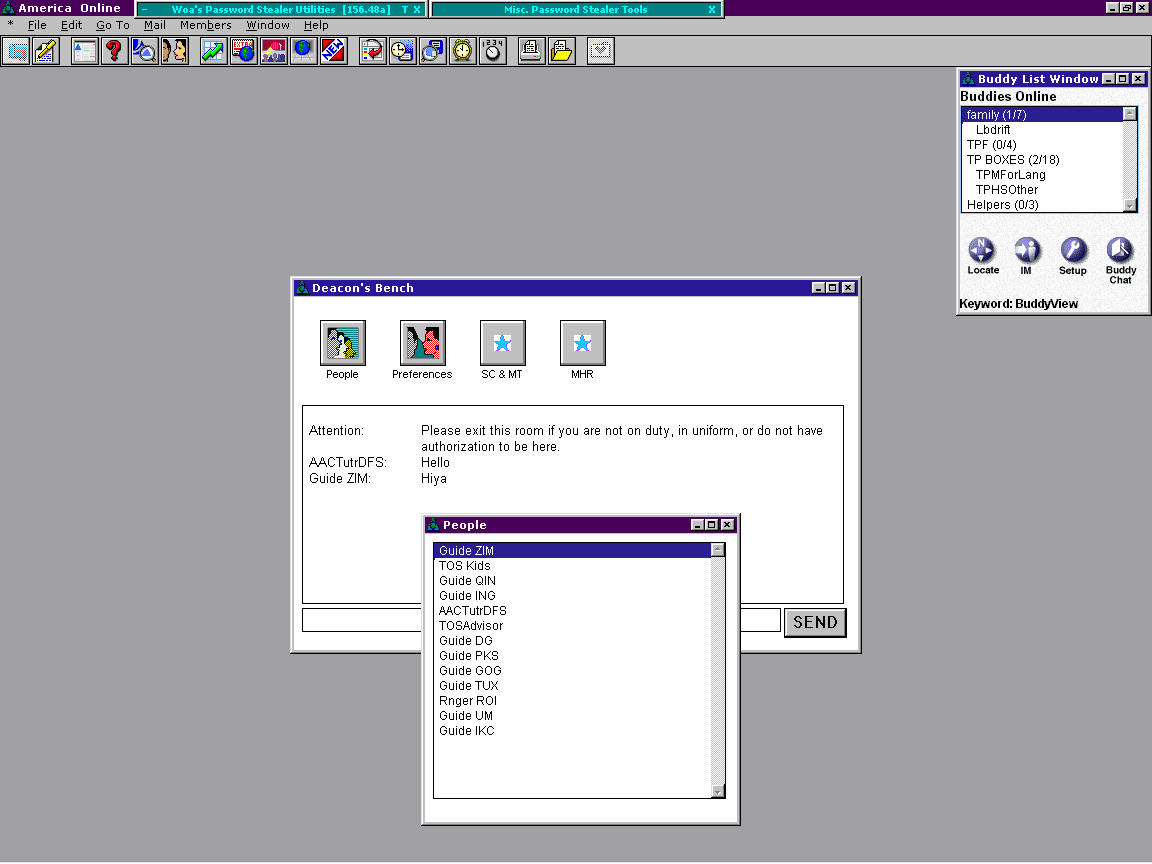
AOL/AIM Exploits
September 9, 2019
August 5, 2019
August 5, 2019
January 25, 2019
January 17, 2018
January 17, 2018
January 5, 2018
January 5, 2018
November 28, 2017
October 10, 2017
October 10, 2017










![Bust -A- Room [Read Me]](http://justinakapaste.com/wp-content/themes/dashscroll/img/thumb-small.png)